Your Password Is Probably Terrible (A Brutally Honest Security Guide for 2026)
If your password is 'Fluffy2019!' you're not as clever as you think. Here's how to generate, test, store, and protect passwords like someone who's been paying attention.
Let’s play a game. Your password: does it start with a capital letter, end with a number or exclamation mark, and contain a word you could find in a dictionary? If so, congratulations, you’ve just described the first pattern every password cracking tool tries.
Credential theft is still the #1 cause of data breaches. Not sophisticated zero-days. Not movie-style hacking. Just people using “Summer2025!” on fourteen different websites and acting surprised when one gets compromised and suddenly they’re all compromised.
Let’s fix that.
Step 1: Let a Robot Make Your Passwords
Humans are terrible at randomness. We think we’re being clever with “P@ssw0rd” and “MyD0g$Name.” Attackers have dictionaries of exactly these substitution patterns. You’re not fooling anyone.
A password generator creates genuinely random strings that no human brain would produce. Set it to 16+ characters with uppercase, lowercase, numbers, and symbols. A random 16-character password would take billions of years to brute-force with current hardware. Your dog’s name followed by your birth year would take about 3 seconds.
The rules:
- Never reuse passwords. One breach shouldn’t unlock your entire digital life. This is the rule everyone knows and nobody follows.
- 16 characters minimum. Every additional character multiplies cracking difficulty exponentially. Length beats complexity.
- Mix all character types. Letters, numbers, symbols. The full buffet.
- No variations on a theme. “Password1,” “Password2,” “Password3” is not a password strategy. It’s a countdown to getting hacked.
Step 2: Face the Truth About Your Current Passwords
This is the part where you test the passwords you actually use, not the ones you’d use in a hypothetical world where you cared more.
A password strength checker evaluates your password against known attack methods and estimates how long it would survive. Most people discover their “strong” password could be cracked in about the time it takes to microwave a burrito.
Red flags to look for:
- Dictionary words with cute letter substitutions (h4ck3r is not secure, ironically)
- Dates with personal significance (birthdays, anniversaries, the year you graduated)
- Anything shorter than 12 characters
- Anything you’ve used on more than one site
Also check if your email appears in known breach databases. If a password has leaked anywhere, ever, consider it public. Change it everywhere you used it. Yes, everywhere. Yes, right now.
Step 3: Stop Storing Passwords in a Sticky Note
You now have 50 unique, random, 16-character passwords. Nobody can memorize those. This is where a password vault comes in.
A browser-based vault that stores data locally has a real advantage: your passwords stay on your device, not on someone else’s server waiting to star in the next “major data breach” headline. The tradeoff is you handle your own backups. Worth it.
Good vault habits:
- Use a long, memorable passphrase as your master password (“correct horse battery staple” was funny once, but the concept is sound)
- Back up your vault to a separate encrypted drive
- Never, ever share vault credentials through email or chat
Step 4: Two-Factor Everything
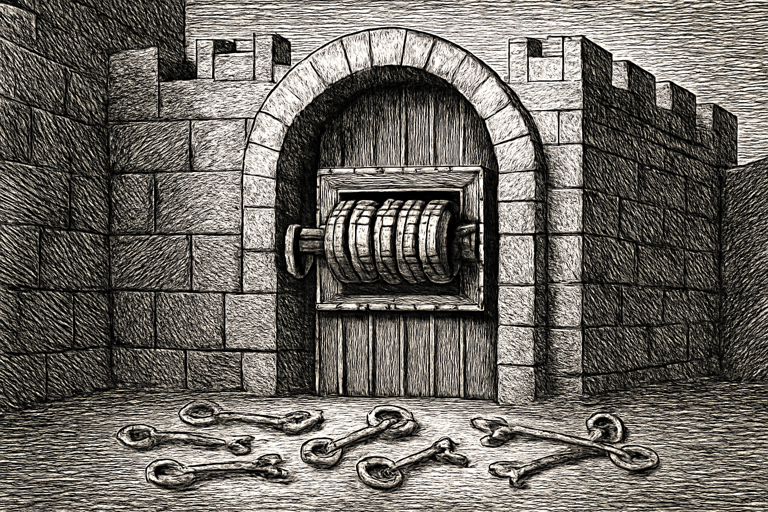
Even a perfect password can fall to phishing, keyloggers, or a server breach you had nothing to do with. Two-factor authentication (2FA) adds a second lock on the door.
Use a two-factor auth tester to verify your 2FA setup works before you’re locked out of your account at 2 AM on a Sunday. Test your primary method and your backup method. Future you will be grateful.
And please, use an authenticator app or hardware key over SMS. SIM-swapping attacks can intercept text messages. Your TOTP app on your phone? That code stays on your device.
Make It a Habit, Not a Project
Password security isn’t something you do once and forget about (like that gym membership you bought in January). Schedule a quarterly check-in:
- Rotate passwords on critical accounts
- Check for new breaches
- Verify 2FA is active on every service that supports it
- Delete accounts you no longer use (fewer accounts = smaller attack surface)
For teams and individuals who want to audit their security posture across multiple services, SCOUTb2 provides tools for ongoing security assessment and monitoring. Because the best time to fix your passwords was five years ago. The second best time is right now.